Known Exploited Vulnerabilities Catalog
Known Exploited Vulnerabilities Catalog - Cisa has removed the following vulnerability from its known exploited vulnerabilities catalog, due to a transcription error: Available as csv and json files. Cisa adds known exploited vulnerabilities to the catalog when there is a clear action for the affected organization to take. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains. Cisa encourages all stakeholders to leverage the cisa catalog of known exploited vulnerabilities and to prioritize these vulnerabilities for immediate remediation. Kev catalog (web) kev catalog (csv) kev catalog (json) kev catalog (json schema) a detailed list of known exploited vulnerabilities.
Kev catalog (web) kev catalog (csv) kev catalog (json) kev catalog (json schema) a detailed list of known exploited vulnerabilities. Cisa encourages all stakeholders to leverage the cisa catalog of known exploited vulnerabilities and to prioritize these vulnerabilities for immediate remediation. Cisa has removed the following vulnerability from its known exploited vulnerabilities catalog, due to a transcription error: Cisa adds known exploited vulnerabilities to the catalog when there is a clear action for the affected organization to take. Available as csv and json files. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains.
Cisa adds known exploited vulnerabilities to the catalog when there is a clear action for the affected organization to take. Available as csv and json files. Cisa has removed the following vulnerability from its known exploited vulnerabilities catalog, due to a transcription error: Cisa encourages all stakeholders to leverage the cisa catalog of known exploited vulnerabilities and to prioritize these vulnerabilities for immediate remediation. Kev catalog (web) kev catalog (csv) kev catalog (json) kev catalog (json schema) a detailed list of known exploited vulnerabilities. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains.
What is the CISA Known Exploited Vulnerabilities (KEV) catalog
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains. Available as csv and json files. Cisa encourages all stakeholders to leverage the cisa catalog of known exploited vulnerabilities and to prioritize these vulnerabilities for immediate remediation. Cisa adds known exploited vulnerabilities to the catalog when.
Known Exploited Vulnerabilities Catalog VulnCheck
Cisa adds known exploited vulnerabilities to the catalog when there is a clear action for the affected organization to take. Cisa encourages all stakeholders to leverage the cisa catalog of known exploited vulnerabilities and to prioritize these vulnerabilities for immediate remediation. Kev catalog (web) kev catalog (csv) kev catalog (json) kev catalog (json schema) a detailed list of known exploited.
CISA adds new vulnerabilities to its Known Exploited Vulnerabilities
Cisa has removed the following vulnerability from its known exploited vulnerabilities catalog, due to a transcription error: Available as csv and json files. Cisa adds known exploited vulnerabilities to the catalog when there is a clear action for the affected organization to take. Kev catalog (web) kev catalog (csv) kev catalog (json) kev catalog (json schema) a detailed list of.
CISA’s Known Exploited Vulnerabilities Catalog by David Vassallo
Cisa adds known exploited vulnerabilities to the catalog when there is a clear action for the affected organization to take. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains. Kev catalog (web) kev catalog (csv) kev catalog (json) kev catalog (json schema) a detailed list.
CISA Adds Cacti Vulnerability To Known Exploited Vulnerabilities
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains. Available as csv and json files. Cisa encourages all stakeholders to leverage the cisa catalog of known exploited vulnerabilities and to prioritize these vulnerabilities for immediate remediation. Cisa has removed the following vulnerability from its known.
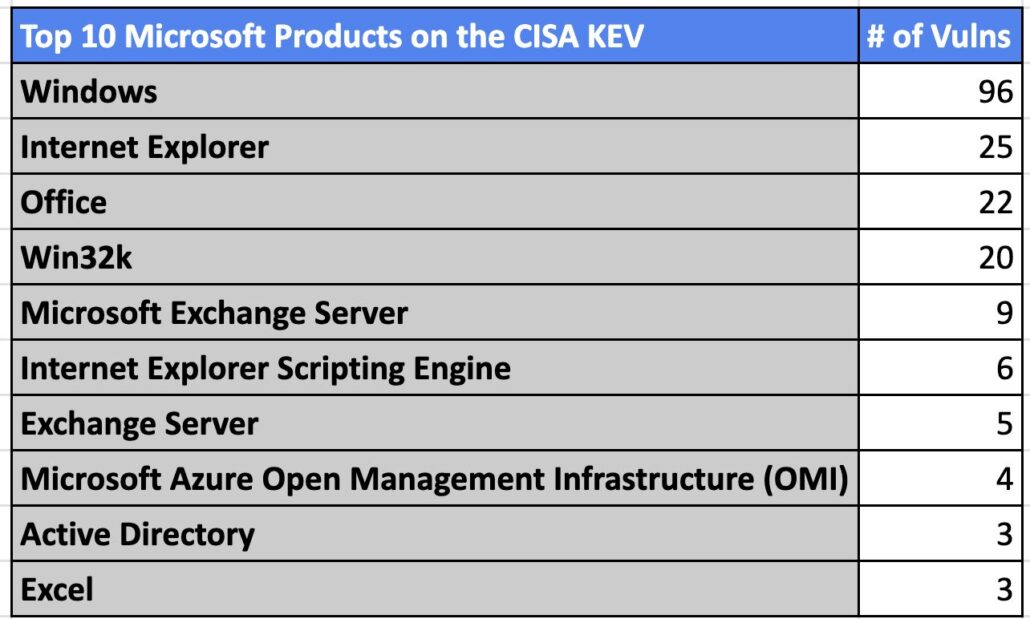
Analyzing 925 Known Exploited Vulnerabilities in the CISA KEV
Available as csv and json files. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains. Cisa adds known exploited vulnerabilities to the catalog when there is a clear action for the affected organization to take. Cisa encourages all stakeholders to leverage the cisa catalog of.
Known Exploited Vulnerabilities Catalog Salmagundi
Cisa encourages all stakeholders to leverage the cisa catalog of known exploited vulnerabilities and to prioritize these vulnerabilities for immediate remediation. Kev catalog (web) kev catalog (csv) kev catalog (json) kev catalog (json schema) a detailed list of known exploited vulnerabilities. Available as csv and json files. For the benefit of the cybersecurity community and network defenders—and to help every.
Catalog of Known Exploited Vulnerabilities
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains. Kev catalog (web) kev catalog (csv) kev catalog (json) kev catalog (json schema) a detailed list of known exploited vulnerabilities. Cisa adds known exploited vulnerabilities to the catalog when there is a clear action for the.
Known Exploited Vulnerabilities (KEV) Catalog By CISA
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains. Cisa encourages all stakeholders to leverage the cisa catalog of known exploited vulnerabilities and to prioritize these vulnerabilities for immediate remediation. Kev catalog (web) kev catalog (csv) kev catalog (json) kev catalog (json schema) a detailed.
CISA Adds Three New Security Flaws to its Known Exploited
Kev catalog (web) kev catalog (csv) kev catalog (json) kev catalog (json schema) a detailed list of known exploited vulnerabilities. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains. Cisa has removed the following vulnerability from its known exploited vulnerabilities catalog, due to a transcription.
For The Benefit Of The Cybersecurity Community And Network Defenders—And To Help Every Organization Better Manage Vulnerabilities And Keep Pace With Threat Activity—Cisa Maintains.
Cisa adds known exploited vulnerabilities to the catalog when there is a clear action for the affected organization to take. Cisa has removed the following vulnerability from its known exploited vulnerabilities catalog, due to a transcription error: Available as csv and json files. Cisa encourages all stakeholders to leverage the cisa catalog of known exploited vulnerabilities and to prioritize these vulnerabilities for immediate remediation.